Date : 1 Mar 2026
The Strategic Imperative of Cyber and Disaster Recovery Planning
2026 Executive Framework for Resilient Enterprises
I. Executive Context: Why This Matters Now


Modern enterprises face compound risk — where cyber incidents, physical disruptions, supply-chain fragility, and regulatory enforcement converge.
-
- WannaCry (2017) disrupted 200,000+ systems globally, crippling healthcare and logistics.
- Hurricane Katrina (2005) caused over $125B in damages and forced permanent closure of thousands of small and mid-sized businesses.
- Colonial Pipeline (2021) demonstrated how a single ransomware incident can disrupt national infrastructure.
- Healthcare ransomware attacks (2020–2024) have increasingly halted clinical operations, impacting patient safety.
Current Risk Landscape (2024–2026 Data)
-
- IBM Cost of a Data Breach Report 2024: Average global breach cost: $4.88 million (up 10% YoY).
- Uptime Institute 2024: 60% of significant outages now exceed $100,000 in cost; 15% exceed $1M.
- NOAA 2023–2024: Record-setting billion-dollar climate events in the U.S.
- World Economic Forum Global Risks Report 2025: Cyber insecurity and extreme weather rank among top systemic global risks.
Executive Thesis
Cyber recovery and disaster recovery (DR) are no longer technical IT functions — they are board-level resilience disciplines that directly influence:
-
- Revenue continuity
- Regulatory standing
- Enterprise valuation
- Insurance posture
- Investor confidence
- Customer trust
Resilience must be measurable, tested, funded, and governed.
II. Definitions, Scope & Time Horizons
1. Cyber Recovery (CR)
Scope: Restoration of IT systems and data following malicious activity (ransomware, insider threat, supply-chain compromise, cloud misconfiguration).
Includes:
-
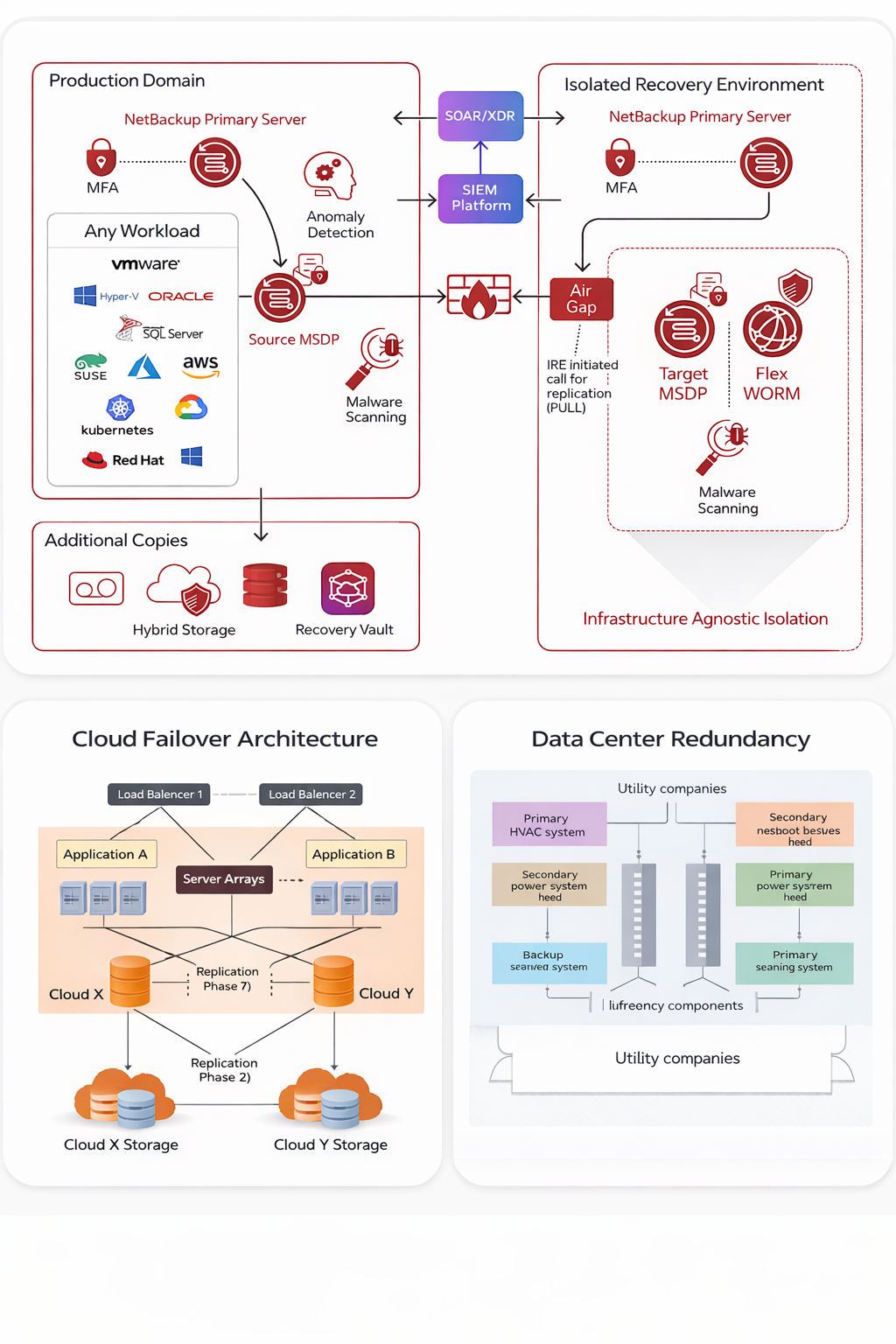
- Immutable backups & air-gapped recovery vaults
- Ransomware isolation environments
- Incident response orchestration
- Forensic validation of clean data sets
- Secure reconstitution of identity systems
Typical Timeline Benchmarks (Mature Program):
-
- Detection: < 24 hours
- Isolation: < 4 hours from confirmation
- Clean recovery environment spin-up: 24–72 hours
- Critical system restoration (Tier 1 apps): 24–96 hours
Framework References:
-
- NIST SP 800-61 Rev. 2 (Computer Security Incident Handling)
- NIST SP 800-184 (Cyber Recovery)
- ISO/IEC 27035
- CISA Ransomware Guide (2023 update)
2. Disaster Recovery (DR)
Scope: Restoration of IT and operational capabilities following non-malicious disruption (natural disasters, power grid failure, infrastructure damage).
Includes:
-
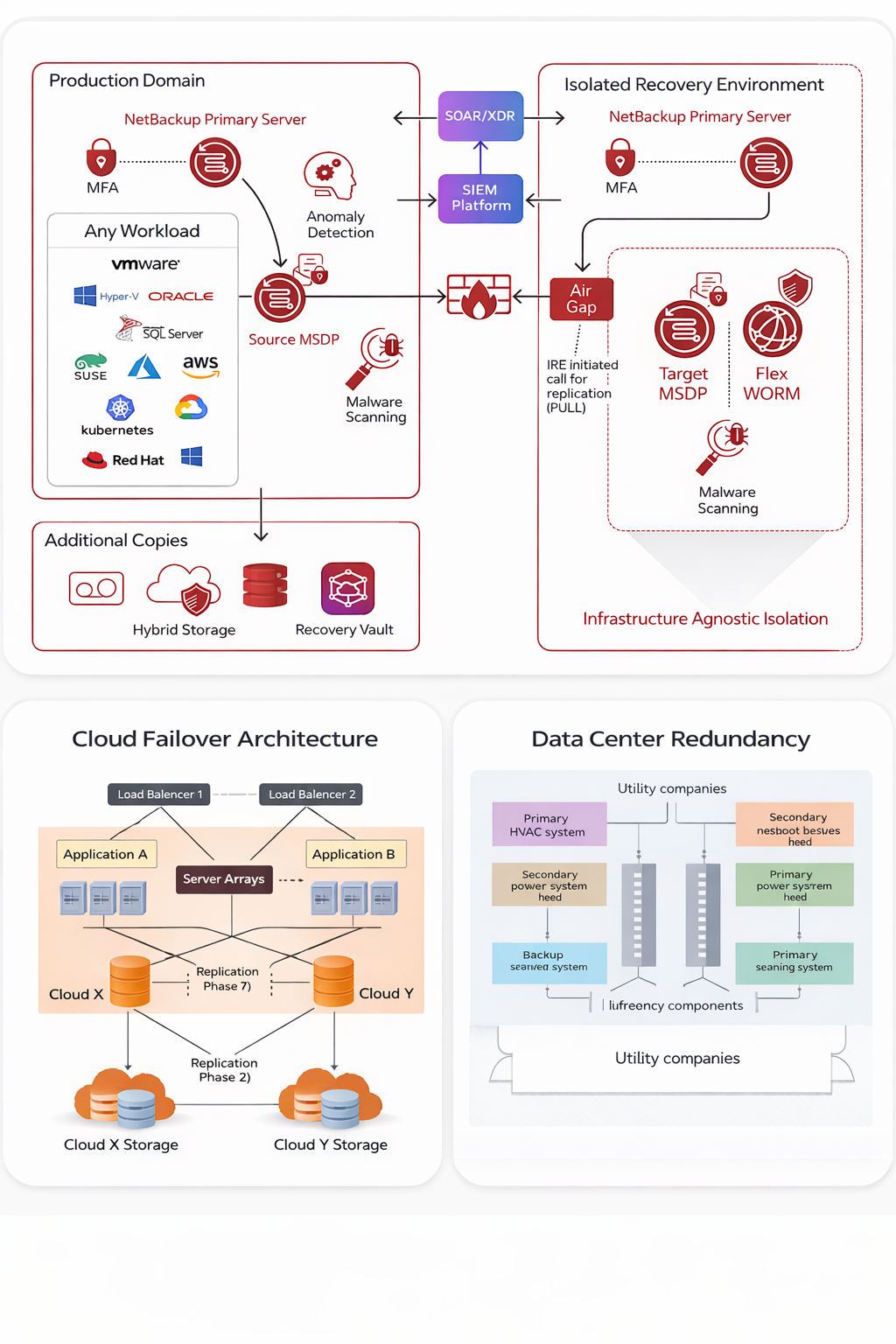
- Secondary/geo-diverse data centers
- Cloud failover architecture
- Backup power systems
- Business continuity sites
- Workforce continuity plans
Typical Timeline Benchmarks (Mature Program):
-
- Failover activation: < 1 hour (automated environments)
- Cloud restoration: 4–24 hours
- Facility-based recovery: 24–72 hours
Framework References:
-
- ISO 22301 (Business Continuity Management)
- NFPA 1600 (Emergency Management Standard)
- FEMA Continuity Guidance Circular
- NIST SP 800-34 (Contingency Planning)
3. Critical Resilience Metrics (Board-Level)
| Metric |
Definition |
Typical Target (Regulated Enterprise) |
| RTO |
Recovery Time Objective |
4–24 hrs (Tier 1 systems) |
| RPO |
Recovery Point Objective |
< 1 hour (mission-critical) |
| MTD |
Maximum Tolerable Downtime |
Defined via BIA |
| MTTR |
Mean Time to Recover |
< 72 hrs |
| Backup Immutability |
% of critical data protected |
100% Tier 1 |
III. Business Case for Investment
1. Business Continuity & Revenue Protection
Downtime directly correlates to revenue loss and contractual exposure.
-
- Capital One breach (2019): 100M+ records exposed; regulatory penalties and reputational impact.
- Healthcare outages (2022–2024) have delayed elective procedures and revenue cycles.
Without structured recovery:
-
- SMEs fail within 6 months post-catastrophic data loss (multiple SBA-referenced studies).
- Cyber insurance claims are increasingly denied where backup hygiene and MFA enforcement are inadequate.
2. Data Protection & Legal Liability
Sensitive data categories at risk:
-
- PHI (HIPAA)
- PII (GDPR, CCPA)
- Financial records (SOX)
- Controlled Unclassified Information (CMMC 2.0)
Regulatory Enforcement Trends:
-
- GDPR fines continue to increase (multi-million Euro enforcement actions in 2023–2024).
- CMMC 2.0 phased implementation (2025–2027) will require verified cyber maturity for DoD contractors.
- SEC Cyber Disclosure Rules (2023 effective; enforcement increasing in 2025).
Failure to recover securely increases litigation risk and regulatory penalties.
3. Financial Exposure Modeling
Direct Costs
-
- Incident response firms
- Legal & notification
- Forensic analysis
- Regulatory penalties
- Business interruption
Indirect Costs
-
- Brand erosion
- Lost contracts
- Increased cyber insurance premiums
- Market cap volatility
Investment in resilience typically costs 5–15% of projected breach impact, yet mitigates > 70% of financial damage when implemented properly.
4. Regulatory & Industry Compliance
| Sector |
Regulatory Drivers |
| Healthcare |
HIPAA, HITECH |
| Financial Services |
FFIEC, SEC, SOX |
| Government Contractors |
NIST 800-171, CMMC 2.0 |
| Global Enterprises |
GDPR, ISO 27001 |
Recovery planning is now audited, not optional.
IV. Integrated Resilience Architecture (Modern Best Practice)
1. Risk Assessment & Business Impact Analysis (0–90 Days)
Scope:
-
- Asset inventory
- Data classification
- Criticality tiering
- Threat modeling
- Financial impact quantification
Deliverables:
-
- Risk Register
- Tiered System Recovery Matrix
- Executive Risk Dashboard
2. Architecture Hardening (3–6 Months)
-
- Immutable, offsite backups (3-2-1-1 model)
- Zero Trust implementation
- MFA & identity segmentation
- Cloud redundancy
- Privileged access monitoring
3. Governance & Response Structure
-
- Defined Incident Commander
- Cross-functional Crisis Management Team
- Board reporting framework
- Legal & PR escalation protocols
4. Testing & Validation (Ongoing)
Testing cadence:
-
- Quarterly tabletop exercises
- Annual live failover test
- Ransomware recovery validation
- Third-party audit review
Continuous improvement cycle:
Detect → Contain → Recover → Analyze → Improve
V. Recommended 12-Month Implementation Timeline
| Phase |
Duration |
Key Outcomes |
| Phase 1: Assessment |
0–90 Days |
BIA, Risk Register, RTO/RPO defined |
| Phase 2: Architecture Upgrade |
3–6 Months |
Immutable backups, DR failover |
| Phase 3: Governance & Playbooks |
6–9 Months |
Formal IR/DR manuals |
| Phase 4: Testing & Audit |
9–12 Months |
Full recovery simulation |
Mature programs reach optimized posture within 12–18 months.
VI. Strategic Outlook (2026–2030)
Emerging Risk Drivers:
-
- AI-powered cyberattacks
- Supply chain infiltration
- Cloud concentration risk
- Climate-induced infrastructure volatility
- Quantum-resistant cryptography transition
Resilience maturity will increasingly influence:
-
- Cyber insurance eligibility
- M&A due diligence
- Enterprise valuation
- Government contract awards
VII. Executive Conclusion
Resilience is not a technical checklist — it is a strategic operating capability.
Organizations that:
-
- Quantify impact,
- Architect layered recovery,
- Test aggressively,
- Govern at the board level,
will outperform peers in crisis events.
Those who fail to operationalize recovery risk:
-
- Regulatory action
- Financial impairment
- Loss of trust
- Permanent operational damage
In today’s operating environment, resilience is a competitive differentiator.